Tips to outwit hackers that are finding new ways to pull old cons
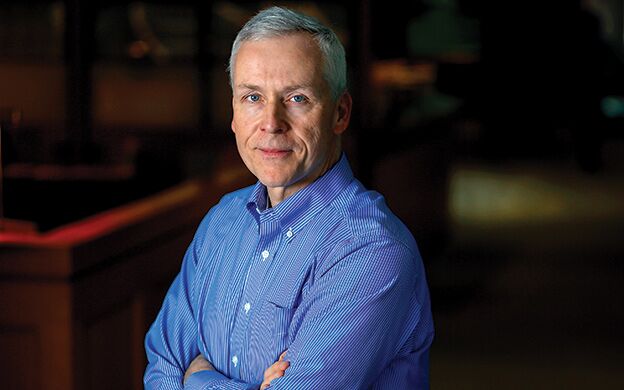 Photo / Tim Greenway
Daniel Mitchell, a Portland-based partner with Bernstein Shur who co-chairs the law firm's litigation and dispute resolution practice group and data security team, warns businesses that email fraud “happens all the time.”
Photo / Tim Greenway
Daniel Mitchell, a Portland-based partner with Bernstein Shur who co-chairs the law firm's litigation and dispute resolution practice group and data security team, warns businesses that email fraud “happens all the time.”
Say you work in accounts payable at a widget maker in Wiscasset and get an urgent email from the company's CEO instructing you to wire money by the end of the day to a designated account. What do you do?
While most people would probably check directly with management before transferring any funds, a small percentage would proceed without realizing that the email came not from the manager, but an imposter. That's the bet fraudsters make when they tweak email addresses and malware-infected web links to appear legitimate, save an extra letter that goes unnoticed.
CEO email fraud “happens all the time,” says Daniel Mitchell, a Portland-based partner with Bernstein Shur who co-chairs the law firm's litigation and dispute resolution practice group and data security team. He explains that hackers will do research on a company, dummy up an email address “very close” to the real thing, and request a money transfer. “Seven times out of 10 the person will say, 'I'm not sure,' but three times out of 10, they'll go ahead and do it.”
Another spoofing technique involves sending an email that looks like it's from a company executive to payroll or human resources requesting a list of employees and their W-2 forms. When the recipient replies, the information goes directly to the cybercriminal. Both scams fall into a common fraud category known as social engineering.
“Hackers will use social engineering techniques to get information. They don't have to get it from some sophisticated way into a computer system,” Mitchell says. “Even at organizations that train people, employees still click on email links they shouldn't.”
'Easy prey' for attacks
About one out of four small businesses surveyed by the Better Business Bureau in 2016 said they had suffered one or more cyberattacks that affected their business in the preceding 12 months. The report found that cybercrime is growing rapidly, costing the global economy more than $400 billion a year.
Industries including manufacturing, real estate and construction reported the highest incidence of attacks, resulting in an average loss per company of $4,387 and up to $150,000. The authors concluded that while the risk was lowest for businesses with 10 employees or less, the danger is still present.
Despite growing awareness of online threats, seven out of 10 businesses surveyed considered an attack unlikely in the next 24 months, leading to a “false sense of safety” the report attributed in part to a lack of expertise and information. It also pointed to common misconceptions like believing the bank would cover a substantial loss if credentials were stolen, when it fact the burden of proof lies with the business.
Small businesses are “easy prey” for cybercriminals, says Bill P. Fanelli, chief security officer with the Council of Better Business Bureaus in Arlington, Va. He says this is partly because while large businesses spend more overall on cybersecurity, smaller firms have to spend more per employee. “The second hurdle is that a larger business has got the resources to figure out all the things they need to do, even if it didn't cost them more.”
Both these factors make small businesses more vulnerable to attacks, especially with increasing digitalization. “Ten years ago it was a manual process, so the bad actors wouldn't necessarily spend the time on a small business,” Fanelli says. Now that everything is automated, “it doesn't matter anymore … Whether I get 100 million customer records in a huge data breach, or 100 over here and 200 over there, I can sell each one of those records for 10 to 50 bucks apiece.”
Phone phishing also remains a danger, with two Maine hospitals, MaineGeneral Medical Center in Augusta and Redington Fairview General Hospital in Skowhegan, both recent victims of scams. Although statewide statistics are hard to come by, Sgt. Kyle Willette of the Maine State Police Computer Crimes Unit said that credit card fraud and card 'skimming' scams are frequent. “We're not a primary investigative agency,” he says, “but a lot of times businesses will call us.”
Defense strategies
Some companies have responded to growing online threats by writing paper checks. That includes Patco Construction Co. Inc., a small property development and contractor business in Sanford, in the wake of a high-profile case of a few years ago. The dispute centered on $588, 851.26 in fraudulent withdrawals from Patco's bank account after the perpetrators supplied Patco's customized answers to security questions.
Although the bank's security system flagged each transaction as unusually “high-risk,” it did not notify the customer about the activity and allowed the payments to go through. The bank was able to block or recover $243,406.83, leaving Patco with a $345,444.43 residual loss. The U.S. District Court in Maine ruled in favor of the bank, only to be reversed by the U.S. Court of Appeals for the First Circuit in Boston. Judges left open the question of what, if any, obligations or responsibilities the Uniform Commercial Code imposed on Patco.
Today, Patco writes only paper checks, said Bernstein Shur's Mitchell, who represented the company. “In some ways they certainly give up something by doing that,” he says, “but they felt it was a more secure solution.”
Companies that prefer checks should either buy secure checks or opt for a fraud-detection service known as 'positive pay,” suggests Frank W. Abagnale Jr., a former con artist now working for the FBI and as a cybercrime consultant. He was recently in Portland to raise awareness about scams and fraud as part of his ongoing work with the AARP Fraud Watch Network. He also recommends using a micro-cut shredder to turn paper into confetti the size of a rice grain.
“When you use a straight ribbon shredder, at the FBI we put those back in less than 30 minutes,” he recently told Mainebiz. “If we can do it, so can a criminal.”
Fanelli has two further tips: Never re-use passwords, and train employees on how to recognize phishing emails. “It's a no-brainer in security circles. You will get a tremendous benefit for a relatively small expense.”






Comments