
Cybercrime is here to stay. Layered security is key
A year ago, a Maine business was hit by ransomware for two days and was forced to pay up in order to get its information back.
“They had systems in place so that they could maintain payroll and keep their business going, so they survived without any major impact,” says Rick Simonds, chief operating officer for Sage Data Security in Portland. “But after the attack, they reassessed their business and strengthened their controls.”
It's a short and simple anecdote, but it just about sums up what cybersecurity experts say about protecting a business in today's inescapable reality of cybercrime: Be proactive and institute a strategy of layered security. Simonds and other experts say layered security comes from three directions.
- First, there are preventive measures, things like strong password policies, strengthening firewall controls and training employees not to click on suspicious links.
- Organizations should also assume there will be a breach, given the ever-evolving sophistication and sheer number of attacks. So the additional measure of data backup is key.
- There are measures that can help identify where an attack originated in the organization's network, so that compromised systems can be identified and quarantined. This gets more sophisticated and involves expert network analysis to identify abnormal behavior in the system.
In the ever-evolving world of cybercrime, security is a full-time task that grows more demanding, specialized and sophisticated every day, says Simonds.
“The best thing to do is to be proactive,” he says. “Plan ahead, and plan for the worst.”
Zero day is here to stay

While the big headlines are about massive breaches that occur at big-box retailers and banks, and the global infections of ransomware like WannaCry and Petya, cybercrime is everywhere, all the time and can hit any business or institution large or small, the experts say.
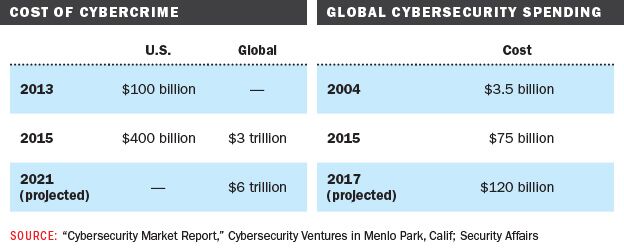
Steve Morgan, founder and CEO of Cybersecurity Ventures in Menlo Park, Calif., estimates that the cost of cybercrime in the United States skyrocketed from $100 billion in 2013 to $400 billion, citing “the legions of hackers-for-hire, and the more sophisticated cyber-attacks launching at businesses, governments, educational institutions and consumers globally.”
The answer, say Maine experts, no longer lies solely in preventive strategies — like antivirus software and firewalls — although those are still essential. But additional, layered strategies are key to quickly identifying and thwarting so-called zero-day attacks — a term for when hackers exploit software vulnerabilities that are unknown to the vendor and which have no known fix.
Layered strategies, experts agree, include measures like continuous network and database monitoring for abnormal behavior, along with trusted data backup, written policies around data protection and device usage and training employees to know what to look for in suspicious activity.
Traditionally, companies buy security products like firewalls, antivirus and software intrusion-prevention systems to try to ward off attacks, says Bob Noel, director of marketing and strategic partnerships for security provider Plixer in Kennebunk. And those tools are beneficial, he adds.
“But if you have the mindset that these technologies alone will keep you safe, that's where your thinking is flawed,” he says. “Organizations must begin to understand that breaches are inevitable. Instead of focusing efforts only on preventative measures, they need to invest in technology and processes that focus on incident response. They need to have the tools, systems, and resources in place so that when these inevitable bad things do happen, the organization can quickly identify and resolve the problem.”
There's no all-in-one solution for detecting and fixing every breach, says Noel. Instead, companies like Plixer provide network traffic monitoring and security analytics that allow analysts to monitor every conversation and understand how users and applications normally behave. This allows them to detect deviations in behavior caused by zero-day attacks.
“Every company in the world has networks that connect computer systems, people and applications,” says Noel. “Every piece of information the business cares about runs across that network. That network infrastructure is the best place to compile and analyze data about what's happening on the network.”
In that analysis, he says, “We provide a rich database that gathers and correlates information such as source and destination IP address, username, application details, web domain, Secure Socket Layer [encryption technology] certificate information and domain name service details, along with thousands of other data elements for every conversation on the network. Then we look for anomalous behavior — things that are out of the ordinary.”
Plixer's software identifies whether a device has communicated with a malicious domain such as a “command-and-control” server, which hackers use to communicate with infected computing devices or members of a “botnet,” a network of computers controlled without the owner's knowledge.
Delivering the context around the suspicious activity, Noel says, makes it easier to pinpoint what happened, and to stitch forensic data together in order to identify affected devices quickly.
“Then I can take the machine offline, wipe the machine clean and reset it,” he says.
Small businesses are at risk
Attacks can be opportunistic or targeted, says Noel. Either way, companies should not be complacent.
“Many organizations say, 'Oh, I'm not that important. No one cares about me enough to target me,'” he says. “Sometimes that's true. However, often it's not. Your data is everything. If you lose it and it's irretrievable, it can put you out of business, which means you will likely be willing to pay to get it back.”
Opportunistic botnets are even scarier, he says.
“They're scanning the internet, and they're launching attacks on devices, not because a human said, 'I'm going to go after this business,' but simply because they're looking for devices that are not patched appropriately,” he says. “You have to worry about that, no matter how small your business is. And it's happening millions and billions of times on a daily basis. It doesn't matter who you are: They're looking for ways to get in, to lock up your data, because they want your money. And they don't care where the money comes from.”
Mark Benton, director of product management at Systems Engineering in Portland, agrees that small businesses are at risk.
“They think the bad guys are after the bank because that's where all the money is,” Benton says. “Not really. There's plenty of evidence that a lot of attacks are on organizations of less than 100 seats. And spam phishing is very opportunistic. They only have to have one hit to be making money.”
The tools to address the issue start with a written cybersecurity policy, he says.
“It's not ideal to deploy technology solutions if you don't know what policies you're trying to implement,” he says. “It varies — whether you're a bank or a health care organization or a manufacturer of high-end devices. You'll have different data you'll want to protect.”
A good security policy, says Benton, categorizes the kind of data a company works with and how it should be treated — considerations such as who has access, how data are communicated internally and outside the organization, and encryption protocols.
Security awareness training is also key, he says. It comes down to the human factor.
“Phishing emails are quite good, and if you have that one person who clicks on anything, you'll get hacked,” he says. “Training tries to build in through the organization, 'Here's what you look for in a suspicious email. Here's what you look for in a link or website.'”
Experts say the problem will only grow.
“It's always a game of cat and mouse, and it seems the good guys are playing catch-up all the time,” says Simonds. “We do a lot to block what the crooks are doing, and they'll figure out how to up their game and find a new way around it. Now you have nation-states with unlimited budgets and manpower and brilliant people. It's a challenge. I don't see it going away.”








Comments